- Incident Response
Incident Response
When you experience a breach, time is crucial. Our 24/7 Security Operations Center responds immediately with precision to eliminate the threat and restore operations.

- ShadowSpear (24/7 SOC)
ShadowSpear® (24/7 SOC)
ShadowSpear® is an unparalleled resource that defends your organizations against advanced cyber threats and attacks 24/7/365.

- Advisory Services
- Risk Assessments
- Vulnerability Assessments
- Security Program Development
- Adversary Services
- Threat Hunting
Advisory Services
Your organization has cybersecurity weaknesses and vulnerabilities you don’t yet even know about. They need to be found and found immediately. If you don’t someone else will.






- Industries












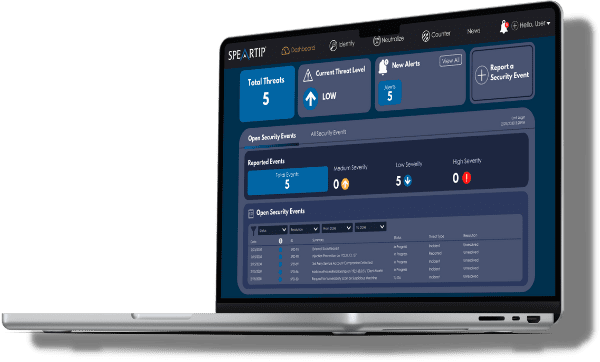


















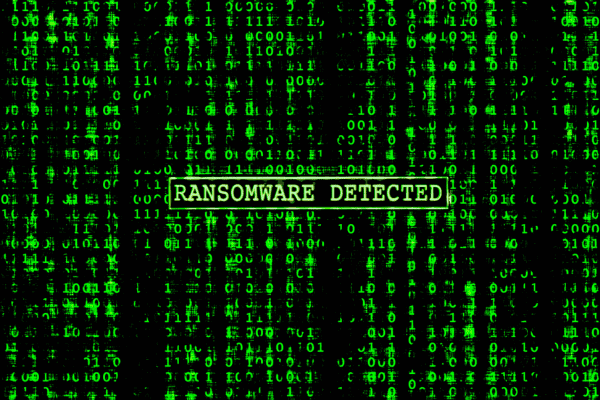


















ShadowSpear supplied us with a complete security package for our cloud. I call it SOC-in-a-box. They came as a complete package to monitor threats and vulnerabilities. So, it replaced any tool we would’ve used. We did not purchase a SIEM; we’re using ShadowSpear. We did not purchase network monitoring software; we’re using ShadowSpear. We did not purchase additional scanners; we’re using ShadowSpear. All of those things that make up an incident response and threat and vulnerability management team in the cloud is for us, ShadowSpear.
Director of Threat and Vulnerability Management, Financial Services